IP Spoofing PPT Presentation Seminar with Pdf Report Free Download: An IP (Internet Protocol) address is the address that reveals the identity of your Internet service provider and your personal Internet connection. IP Address spoofing – a technique that emerges with the usage of the internet. It is used by hackers to mantle the identity of other computing systems and modify the address of source internet protocol to create packets over the network.
Also See: Latest Seminar Topics for Computer Science
Communication between systems is carried out in a way by upstream and downstream data packets through the modern internet. These packets contain the requested information along with routing statistics that primarily includes source and destination IP address. Throughout the process, if packets are spoofed then the source addressed is fetched by the illegal users. It is not limited to the internet, but also applicable to other hardware and software components such as e-mails, phone calls or websites.
Also See: Technical IEEE Seminar Topics for CSE
IP Spoofing PPT Presentation Seminar with Pdf Report Free Download
This page contains IP Spoofing Seminar and PPT with pdf report for free download. get the link at the end of this article.
Working with IP Spoofing?
Bifurcate the IP address and the packet will give the entire information to the wrong IP address. A Normal scenario of request execution for web pages initiates by a web server when originating workstation starts sending the packet of 12 bytes with required information out of which 8 bytes indicate the source IP address A Web server uses the source IP address as the destination and its IP address as a source address.
It can be better explained with the help of an illustration:
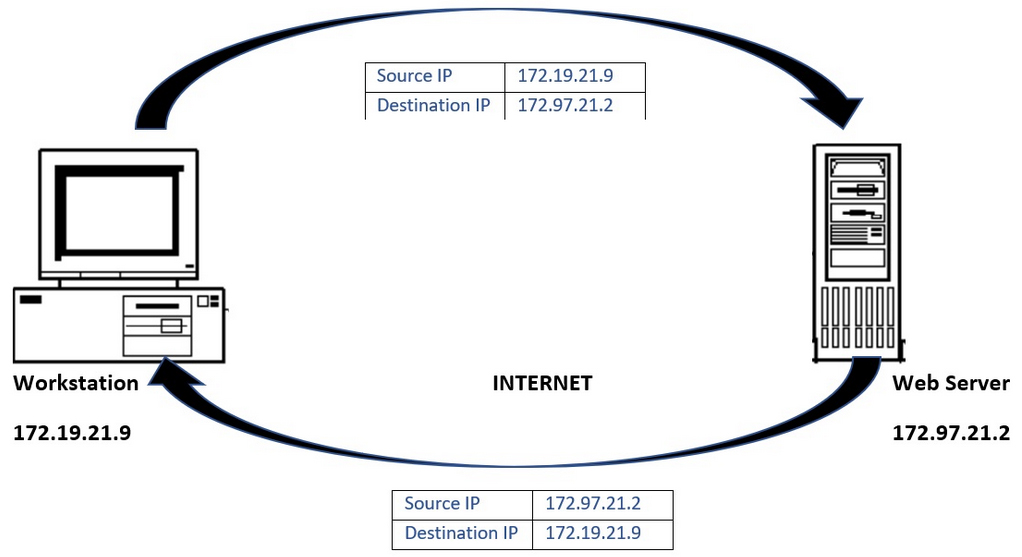
The above diagram represents the normal flow of the data request and server response.
Data flow in case Spoofing IP:
In the case of Spoofing, the web server will send the requested server pages to the spoofed IP address which is originating workstation as per server.
Also See: Cloud Computing Ppt
Network access through Spoofed address:
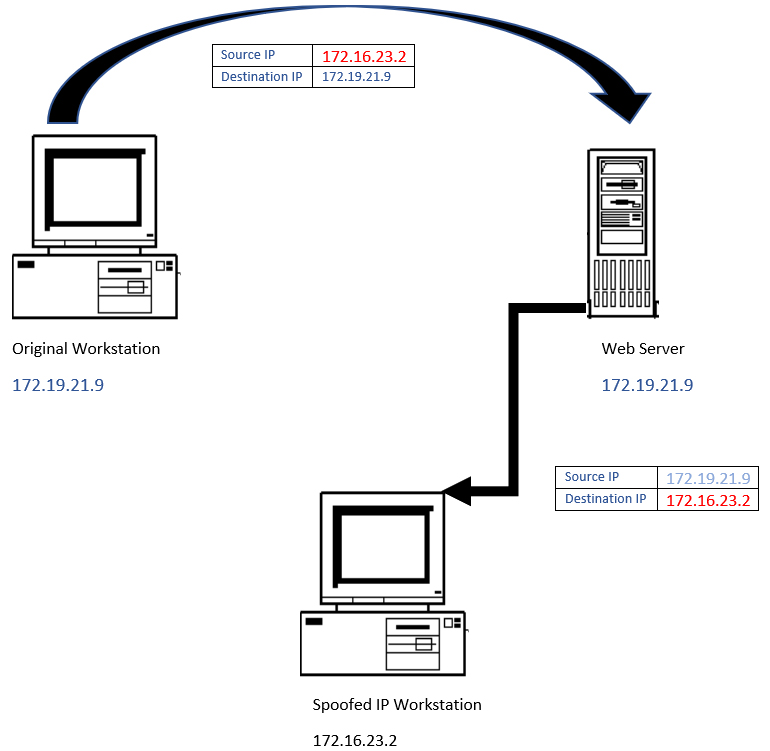
The above diagram indicates that the original workstation is out from the sending and receiving process and data packets are targeted to the spoofed system.
Spoofing Attacks
- Non-Blind Spoofing
- Blind Spoofing
- Man in the Middle Attack
- Denial of Service Attack
Why IP Spoofing is Used
- These are attacks that relate massive amounts of information being sent to computers over a network in an attempt to crash the full network.
- The hacker does not get caught because the origin of the messages cannot be determined due to the bogus IP address.
Also See: Blue Brain Seminar PPT with Pdf Report
Types of IP Spoofing:
Spoofing can be done by using different communication mediums or internet interfaces. Below are the common types of spoofing techniques used by attackers:
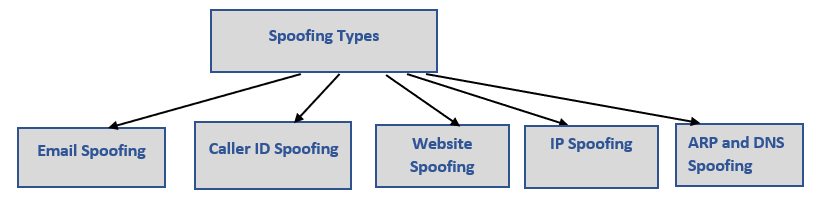
| Type of Spoofing | Implementation |
| Email Spoofing | It is the most common way to steal someone’s personal information and misuse it for obvious reasons. Emails are sent by using IP address similar to famous websites to force the user to open the link and to feed the information to proceed further. These emails contain information viruses, malware or malevolent website addresses.
|
| Caller ID Spoofing | Attackers are calling from numbers that appeared trusted websites or from financial bodies to ask information about financial details of the person such as bank account information, CVV, card details, etc.
|
| Website Spoofing | New Websites are created, which are replicas of original ones and trusted by users. Attackers use them as an interface to get information by hiding their original system.
|
| IP Spoofing | The agenda of this spoofing is to access the network on which user-based authentication is active and modifying the IP address is the way to enter into those networks.
|
| ARP and DNS Spoofing | Address resolution protocol is used to resolves IP conflicts and the attacker can connect to an authorized data network. Domain Name system spoofing refers to the distribution of network traffic to different IPs which are giving an option to attackers to spread malware. |
Also See: Nanotechnology PPT
Protection against Spoofing Attacks:
- Never open the emails with familiar keywords related to your personal data or professional. Delete the emails that contain lucrative monetary deals and asking for financial data.
- Don’t click on the attachments sent by using a suspicious email address that contains unusual sentence formation and or URLs provided to upload information.
- Avoid calls from illegitimate numbers which seems to be important contact such as employment opportunity, winning lotteries, and never share information with the caller if the call is picked.
- In addition to the above, the system is also vetting the information before processing the web requests from workstations by using multi-layer architecture. The Transmission control protocol is using sequence number technique with a workstation to ensure receiving packets are sent by the original connection.
- Packet and ingress filtering are the techniques that are used to block the packet from unreliable sources which block outsiders from attack internal machines.
Advantages of IP Spoofing
- Multiple Servers
- Transparent Proxying
Also See: Mobile Phone Cloning Seminar PPT with Pdf Report
Disadvantages of IP Spoofing
- Blind to Replies
- Serial attack platforms
Content of IP Spoofing PPT Presentation Seminar with Pdf Report Free
- Introduction
- What is IP Spoofing
- How IP Spoofing Works
- Why IP Spoofing is Used
- History
- Applications
- Spoofing Attacks
- Advantages
- Disadvantages
- Future Scope
- Conclusion
Here we are giving you IP Spoofing Seminar and PPT with PDF report. All you need to do is just click on the download link and get it.
IP Spoofing PPT and Seminar Free Download
IP Spoofing pdf Report Free Download
It was all about Embedded Systems Seminar and PPT with pdf report. If you liked it then please share it or if you want to ask anything then please hit comment button.