In modern internet infrastructure, an IP address functions as a persistent technical identifier. It allows websites to associate logins, page views, clicks, and repeated requests with a single source. This is why proxy infrastructure — including services provided through platforms such as buy proxy server — has become a standard technical layer in professional online operations rather than a niche tool. When multiple actions originate from the same IP address, platforms treat them as related by default, even when they belong to different accounts or users.
This linkage is not theoretical. Connection-level signals remain among the most widely used indicators for traffic classification, automated behavior detection, and risk assessment. As activity accumulates from a single source, platforms typically respond by slowing requests, introducing additional verification, or imposing restrictions.
Proxy servers are designed to disrupt this accumulation.
Instead of connecting to a website directly, traffic is routed through an intermediary server. As a result, the website sees the proxy’s IP address rather than the user’s real one. For the user, the experience remains unchanged: pages load normally, accounts operate as expected, and data is transferred without visible friction. For the website, however, the interaction is now attributed to a different connection.
A proxy does not make activity invisible. It does not eliminate tracking or override platform rules. Its function is narrower and more structural: separating connections and removing unnecessary technical links between actions. This is precisely why proxies are widely used in legitimate workflows, including testing, analytics, advertising operations, and structured account management.
How a Proxy Server Works
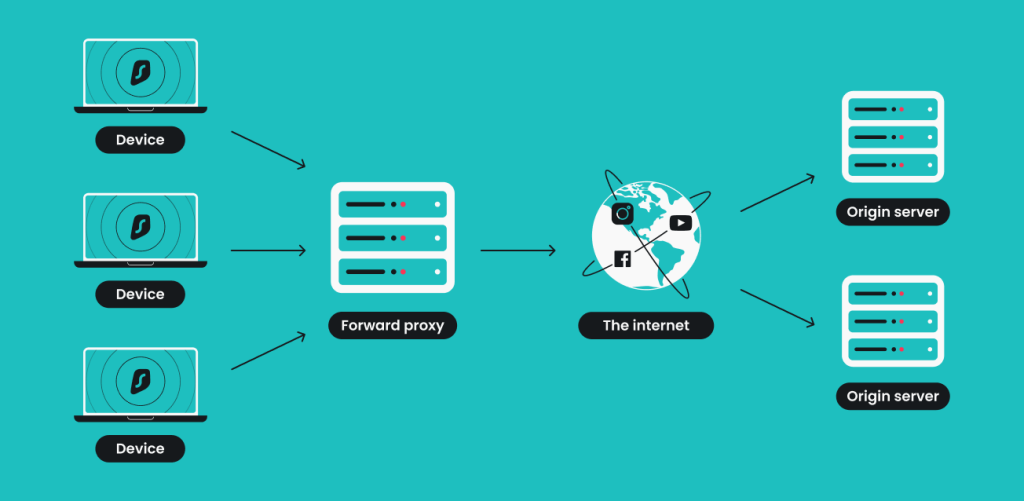
From a technical perspective, a proxy server introduces an additional step into the connection chain:
User → Internet provider → Proxy server → Website
When a proxy is enabled, a request does not reach a website directly. It is first sent to the proxy server, which forwards it using its own IP address. The website responds to the proxy, and the proxy then delivers the response back to the user.
On the surface, nothing changes. Pages load, sessions persist, and data flows normally. From the website’s perspective, however, the source of the request is no longer the original device. This distinction becomes critical in environments where platforms monitor repeated interactions and correlate them at the network level.
Why Proxy Servers Are Used in Practice
Proxies are rarely adopted proactively. In most cases, they become necessary when direct connections begin to create operational friction.
Managing Multiple Accounts
Platforms that host user accounts closely monitor where logins originate. Even when accounts are independent, repeated access from the same IP address creates a technical link between them. Over time, this can lead to additional verification requirements, reduced functionality, or outright restrictions.
Proxy servers allow these connections to be separated so that each account appears to originate from a distinct device and network. This is one reason why organizations sourcing proxy infrastructure through services like buy proxy server typically combine IP separation with additional isolation mechanisms rather than relying on IP substitution alone.
The Role of Browser Isolation
A common mistake is using a proxy within a standard browser. In this configuration, the IP address changes, but all other parameters remain identical: browser settings, device fingerprints, cookies, and session behavior.
Anti-detect browsers address this limitation by creating isolated browser profiles. Each profile functions as an independent environment with its own storage, configuration, and behavioral signals. When a separate proxy is assigned to each profile, connections no longer intersect at either the network or browser level.
This approach is widely implemented using tools such as Multilogin, which combine browser isolation with built-in proxy management. In practice, this establishes a simple and predictable structure: one account, one browser profile, one proxy connection.
Data Collection and Parsing
Collecting data from websites is a routine task for analysts and marketing teams. Prices, product availability, catalogs, and descriptions are updated continuously. Issues arise when all requests originate from a single connection.
As request volume accumulates on one IP address, websites may throttle responses, introduce delays, or restrict access altogether. Proxy servers distribute requests across multiple connections, reducing load concentration and allowing data collection to proceed more consistently.
When combined with isolated browser environments or professionally managed proxy pools, this approach also improves session stability and reduces errors caused by overlapping requests.
Advertising Verification and Testing
Advertising content is not static. It can vary depending on device characteristics, traffic sources, and connection attributes. Without proxies, testing often reflects only a single scenario tied to one connection.
Proxy servers make it possible to view advertising content as different users would see it, enabling verification of real impressions and comparison of variations. When each testing scenario runs inside an isolated browser profile, campaigns can be evaluated without session conflicts or data contamination.
Accessing Region-Specific Website Versions
Many websites dynamically adapt content based on the perceived location of a connection. Language versions, pricing displays, promotional offers, and available features may differ depending on how a user is identified.
Proxies with location attributes allow teams to view websites as users from specific regions would experience them. This capability is commonly used for interface testing, market analysis, and validation of localized content without modifying the website itself.
Types of Proxy Servers and Their Differences
Choosing a proxy type directly affects stability, error rates, and operational predictability. The same workflow may perform reliably with one type of proxy and fail repeatedly with another.
Residential Proxies
Residential proxies use IP addresses assigned to real household internet connections. To websites, these connections resemble ordinary users accessing the internet from personal devices.
Because of this, residential proxies are commonly used for long-running sessions, sensitive accounts, and workflows where activity must appear natural and consistent. Their primary advantage is credibility rather than speed.
Datacenter Proxies
Datacenter proxies operate on server infrastructure and are not associated with real users. They are typically fast and cost-effective, which makes them suitable for technical testing and automation.
Their main limitation is reputation. Many datacenter IP addresses have been used extensively and may already appear on blocklists or trigger heightened scrutiny on platforms with strict monitoring systems.
Mobile Proxies
Mobile proxies route traffic through IP addresses used by mobile networks. These IPs rotate frequently and are shared among large numbers of real users, making them appear highly trustworthy from a platform’s perspective.
They are often used in scenarios where other proxy types lose effectiveness. The trade-offs include higher cost, variable speed, and more complex session control.
ISP Proxies
ISP proxies sit between residential and datacenter proxies. While technically hosted on servers, they are registered with internet providers rather than data centers.
This structure offers a balance of stability, speed, and perceived legitimacy, making ISP proxies suitable for long-term, predictable workflows.
Conclusion
A proxy server is not a shortcut or a workaround. It is a structural component that changes how online connections are attributed and interpreted. Used correctly, proxies reduce unintended linkages, limit signal accumulation, and create more predictable technical environments.
When combined with proper browser isolation and well-chosen proxy infrastructure, proxies do not complicate workflows — they make them more controlled, stable, and scalable.